Tailored Access Operations

The Office of Tailored Access Operations (TAO) is a cyber-warfare intelligence-gathering unit of the National Security Agency (NSA). It has been active since at least circa 1998.[1][2] TAO identifies, monitors, infiltrates, and gathers intelligence on computer systems being used by entities foreign to the United States.[3][4][5][6] The NSA terms these activities "computer network exploitation".
TAO is reportedly "now the largest and arguably the most important component of the NSA's huge Signals Intelligence Directorate (SID)[7] (SIGINT), consisting of more than 1,000 military and civilian computer hackers, intelligence analysts, targeting specialists, computer hardware and software designers, and electrical engineers."[1]
A document leaked by former NSA contractor Edward Snowden describing the unit's work says TAO has software templates allowing it to break into commonly used hardware, including “routers, switches, and firewalls from multiple product vendor lines".[8] According to The Washington Post, TAO engineers prefer to tap networks rather than isolated computers, because there are typically many devices on a single network.[8]
Organization
TAO's headquarters are termed the Remote Operations Center (ROC) and are based at the NSA headquarters at Fort Meade, Maryland. TAO also has expanded to NSA Hawaii (Wahiawa, Oahu), NSA Georgia (Fort Gordon, Georgia), NSA Texas (San Antonio, Texas), and NSA Colorado (Buckley Air Force Base, Denver).[1]
Since 2013, the head of TAO is Rob Joyce, a 25-plus year employee who previously worked in the NSA's Information Assurance Directorate (IAD). In January 2016, Joyce had a rare public appearance when he gave a presentation at the Usenix’s Enigma conference. [9]
In the Remote Operations Center, 600 employees gather information from around the world.[10][11] Their motto is "Your data is our data, your equipment is our equipment - anytime, any place, by any legal means."
- Data Network Technologies Branch: develops automated spyware
- Telecommunications Network Technologies Branch: improve network and computer hacking methods[12]
- Mission Infrastructure Technologies Branch: operates the software provided above[13]
- Access Technologies Operations Branch: Reportedly includes personnel seconded by the CIA and the FBI, who perform what are described as "off-net operations," which means they arrange for CIA agents to surreptitiously plant eavesdropping devices on computers and telecommunications systems overseas so that TAO's hackers may remotely access them from Fort Meade.[1] Specially equipped submarines, currently USS Jimmy Carter,[14] are used to wiretap fibre optic cables around the globe.
Virtual locations
Details on a program titled QUANTUMSQUIRREL indicate NSA ability to masquerade as any routable IPv4 or IPv6 host. This enables an NSA computer to generate false geographical location and personal identification credentials when accessing the Internet utilizing QUANTUMSQUIRREL.[15]
NSA ANT catalog
The NSA ANT catalog is a 50-page classified document listing technology available to the United States National Security Agency (NSA) Tailored Access Operations (TAO) by the Advanced Network Technology (ANT) Division to aid in cyber surveillance. Most devices are described as already operational and available to US nationals and members of the Five Eyes alliance. According to Der Spiegel, which released the catalog to the public on December 30, 2013, "The list reads like a mail-order catalog, one from which other NSA employees can order technologies from the ANT division for tapping their targets' data." The document was created in 2008.[16] Security researcher Jacob Appelbaum gave a speech at the Chaos Communications Congress in Hamburg, Germany, in which he detailed techniques that the simultaneously published Der Spiegel article he coauthored disclosed from the catalog.[16]
QUANTUM attacks
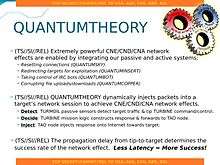
The TAO has developed an attack suite they call QUANTUM. It relies on a compromised router that duplicates internet traffic, typically HTTP requests, so that they go both to the intended target and to an NSA site (indirectly). The NSA site runs FOXACID software which sends back exploits that load in the background in the target web browser before the intended destination has had a chance to respond (it's unclear if the compromised router facilitates this race on the return trip). Prior to the development of this technology, FOXACID software made spear-phishing attacks the NSA referred to as spam. If the browser is exploitable, further permanent "implants" (rootkits etc.) are deployed in the target computer, e.g. OLYMPUSFIRE for Windows, which give complete remote access to the infected machine.[17] This type of attack is part of the man-in-the-middle attack family, though more specifically it is called man-on-the-side attack. It is difficult to pull off without controlling some of the Internet backbone.[18]
There are numerous services that FOXACID can exploit this way. The names of some FOXACID modules are given below:[19]
By collaboration with the British Government Communications Headquarters (GCHQ) (MUSCULAR), Google services could be attacked too, including Gmail.[20]
Finding machines that are exploitable and worth attacking is done using analytic databases such as XKeyscore.[21] A specific method of finding vulnerable machines is interception of Windows Error Reporting traffic, which is logged into XKeyscore.[22]
QUANTUM attacks launched from NSA sites can be too slow for some combinations of targets and services as they essentially try to exploit a race condition, i.e. the NSA server is trying to beat the legitimate server with its response.[23] As of mid-2011, the NSA was prototyping a capability codenamed QFIRE, which involved embedding their exploit-dispensing servers in virtual machines (running on VMware ESX) hosted closer to the target, in the so-called Special Collection Sites (SCS) network worldwide. The goal of QFIRE was to lower the latency of the spoofed response, thus increasing the probability of success.[24][25][26]
COMMENDEER [sic] is used to commandeer (i.e. compromise) untargeted computer systems. The software is used as a part of QUANTUMNATION, which also includes the software vulnerability scanner VALIDATOR. The tool was first described at the 2014 Chaos Communication Congress by Jacob Appelbaum, who characterized it as tyrannical.[27][28][29]
QUANTUMCOOKIE is a more complex form of attack which can be used against Tor users.[30]
Known targets and collaborations
- China[1]
- Tor/Firefox users[18]
- In concert with the U.S. CIA and FBI, TAO is used to intercept laptops purchased online, divert them to secret warehouses where spyware and hardware is installed, and send them on to customers.[31]
- OPEC[32]
- SEA-ME-WE 4 – an optical fibre submarine communications cable system that carries telecommunications between Singapore, Malaysia, Thailand, Bangladesh, India, Sri Lanka, Pakistan, United Arab Emirates, Saudi Arabia, Sudan, Egypt, Italy, Tunisia, Algeria and France.[28]
- Mexico's Secretariat of Public Security[22]
- TAO's QUANTUM INSERT technology was passed to UK services, particularly to GCHQ's MyNOC, which used it to target Belgacom and GPRS roaming exchange (GRX) providers like the Comfone, Syniverse, and Starhome.[22] Belgacom, which provides services to the European Commission, the European Parliament and the European Council discovered the attack.[33]
- Försvarets radioanstalt (FRA) in Sweden gives access to fiberoptic links for QUANTUM cooperation.[34][35]
According to a 2013 article in Foreign Policy, "TAO has become increasingly accomplished at its mission, thanks in part to the high-level cooperation it secretly receives from the 'big three' American telecom companies (AT&T, Verizon and Sprint), most of the large US-based Internet service providers, and many of the top computer security software manufacturers and consulting companies."[36] A 2012 TAO budget document claims that these companies, on TAO's behest, "insert vulnerabilities into commercial encryption systems, IT systems, networks and endpoint communications devices used by targets".[36] A number of US companies, including Cisco and Dell, have subsequently made public statements denying that they insert such back doors into their products.[37] Microsoft provides advance warning to the NSA of vulnerabilities it knows about, before fixes or information about these vulnerabilities is available to the public; this enables TAO to execute so-called zero-day attacks.[38] A Microsoft official who declined to be identified in the press confirmed that this is indeed the case, but said that Microsoft can't be held responsible for how the NSA uses this advance information.[39]
See also
- Advanced persistent threat
- Bullrun (decryption program)
- Computer and Internet Protocol Address Verifier (CIPAV)
- Computer network operations
- Cyberwarfare
- Cyberwarfare in the United States
- DigiNotar
- Equation Group
- FinFisher
- Hacking (disambiguation)
- Magic Lantern (software)
- MiniPanzer and MegaPanzer
- NSA ANT catalog
- PLA Unit 61398
- Stuxnet
- Syrian Electronic Army
- WARRIOR PRIDE
References
- 1 2 3 4 5 Aid, Matthew M. (10 June 2013). "Inside the NSA's Ultra-Secret China Hacking Group". Foreign Policy. Retrieved 11 June 2013.
- ↑ Paterson, Andrea (30 August 2013). "The NSA has its own team of elite hackers". The Washington Post. Retrieved 31 August 2013.
- ↑ Kingsbury, Alex (June 19, 2009). "The Secret History of the National Security Agency". U.S. News & World Report. Retrieved 22 May 2013.
- ↑ Kingsbury, Alex; Anna Mulrine (November 18, 2009). "U.S. is Striking Back in the Global Cyberwar". U.S. News & World Report. Retrieved 22 May 2013.
- ↑ Riley, Michael (May 23, 2013). "How the U.S. Government Hacks the World". Bloomberg Businessweek. Retrieved 23 May 2013.
- ↑ Aid, Matthew M. (8 June 2010). The Secret Sentry: The Untold History of the National Security Agency. Bloomsbury USA. p. 311. ISBN 978-1-60819-096-6. Retrieved 22 May 2013.
- ↑ FOIA #70809 (released 2014-09-19)
- 1 2 Barton Gellman; Ellen Nakashima (August 30, 2013). "U.S. spy agencies mounted 231 offensive cyber-operations in 2011, documents show". The Washington Post. Retrieved 7 September 2013.
Much more often, an implant is coded entirely in software by an NSA group called, Tailored Access Operations (TAO). As its name suggests, TAO builds attack tools that are custom-fitted to their targets. The NSA unit's software engineers would rather tap into networks than individual computers because there are usually many devices on each network. Tailored Access Operations has software templates to break into common brands and models of "routers, switches, and firewalls from multiple product vendor lines," according to one document describing its work.
- ↑ The Register: NSA’s top hacking boss explains how to protect your network from his attack squads, January 28, 2016
- ↑ "Secret NSA hackers from TAO Office have been pwning China for nearly 15 years". Computerworld. 2013-06-11. Retrieved 2014-01-27.
- ↑ Rothkopf, David. "Inside the NSA's Ultra-Secret China Hacking Group". Foreign Policy. Retrieved 2014-01-27.
- ↑ "Hintergrund: Die Speerspitze des amerikanischen Hackings - News Ausland: Amerika". tagesanzeiger.ch. Retrieved 2014-01-27.
- ↑ WebCite query result
- ↑ noahmax (2005-02-21). "Jimmy Carter: Super Spy?". Defense Tech. Retrieved 2014-01-27.
- ↑ "The NSA and GCHQ's QUANTUMTHEORY Hacking Tactics". firstlook.org. 2014-07-16. Retrieved 2014-07-16.
- 1 2 This section copied from NSA ANT catalog; see there for sources
- ↑ "Quantumtheory: Wie die NSA weltweit Rechner hackt". Der Spiegel. 2013-12-30. Retrieved 2014-01-18.
- 1 2 Bruce Schneier (2013-10-07). "How the NSA Attacks Tor/Firefox Users With QUANTUM and FOXACID". Schneier.com. Retrieved 2014-01-18.
- ↑ Fotostrecke (2013-12-30). "NSA-Dokumente: So knackt der Geheimdienst Internetkonten". Der Spiegel. Retrieved 2014-01-18.
- ↑ "NSA-Dokumente: So knackt der Geheimdienst Internetkonten". Der Spiegel. 2013-12-30. Retrieved 2014-01-18.
- ↑ Gallagher, Sean (August 1, 2013). "NSA's Internet taps can find systems to hack, track VPNs and Word docs". Retrieved August 8, 2013.
- 1 2 3 "Inside TAO: Targeting Mexico". Der Spiegel. 2013-12-29. Retrieved 2014-01-18.
- ↑ Fotostrecke (2013-12-30). "QFIRE - die "Vorwärtsverteidigng" der NSA". Der Spiegel. Retrieved 2014-01-18.
- ↑ "QFIRE - die "Vorwärtsverteidigng" der NSA". Der Spiegel. 2013-12-30. Retrieved 2014-01-18.
- ↑ "QFIRE - die "Vorwärtsverteidigng" der NSA". Der Spiegel. 2013-12-30. Retrieved 2014-01-18.
- ↑ "QFIRE - die "Vorwärtsverteidigng" der NSA". Der Spiegel. 2013-12-30. Retrieved 2014-01-18.
- ↑ ""Chaos Computer Club CCC Presentation" at 28:34".
- 1 2 Thomson, Iain (2013-12-31). "How the NSA hacks PCs, phones, routers, hard disks 'at speed of light': Spy tech catalog leaks". The Register. London. Retrieved 2014-08-15.
- ↑ Mick, Jason (2013-12-31). "Tax and Spy: How the NSA Can Hack Any American, Stores Data 15 Years". DailyTech. Retrieved 2014-08-15.
- ↑ Weaver, Nicholas (2013-03-28). "Our Government Has Weaponized the Internet. Here's How They Did It". Wired. Retrieved 2014-01-18.
- ↑ "Inside TAO: The NSA's Shadow Network". Der Spiegel. 2013-12-29. Retrieved 2014-01-27.
- ↑ Gallagher, Sean (2013-11-12). "Quantum of pwnness: How NSA and GCHQ hacked OPEC and others". Ars Technica. Retrieved 2014-01-18.
- ↑ "British spies reportedly spoofed LinkedIn, Slashdot to target network engineers". Network World. 2013-11-11. Retrieved 2014-01-18.
- ↑ "Läs dokumenten om Sverige från Edward Snowden - Uppdrag Granskning". SVT.se. Retrieved 2014-01-18.
- ↑ "What You Wanted to Know" (PDF). documentcloud.org. Retrieved 2015-10-03.
- 1 2 Matthew M. Aid, (October 15, 2013) "The NSA's New Code Breakers", Foreign Policy
- ↑ Farber, Dan (2013-12-29). "NSA reportedly planted spyware on electronics equipment | Security & Privacy". CNET News. Retrieved 2014-01-18.
- ↑ Schneier, Bruce (2013-10-04). "How the NSA Thinks About Secrecy and Risk". The Atlantic. Retrieved 2014-01-18.
- ↑ Riley, Michael (2013-06-14). "U.S. Agencies Said to Swap Data With Thousands of Firms". Bloomberg. Retrieved 2014-01-18.
External links
- Inside TAO: Documents Reveal Top NSA Hacking Unit
- NSA 'hacking unit' infiltrates computers around the world – report
- NSA Tailored Access Operations
- http://www.wired.com/threatlevel/2013/09/nsa-router-hacking/
- http://www.nytimes.com/2014/01/15/us/nsa-effort-pries-open-computers-not-connected-to-internet.html
